If you look into the current crypto hardware wallet market, you’d notice that almost all of them fall into two broad categories, primarily driven by two different ideologies.
On one hand, we have the Trezor-type wallets that follow the open-source ideology of keeping everything open and verifiable. And then, there are the Ledger-type wallets that offer not-so-open bank-grade security, through a (usually EAL5+ certified) Secure Element (SE).

But both of these approaches have ups and downs. A fully open-source system such as Trezor’s generally doesn’t have a secure element. And thus, the secret is usually stored in a general-purpose MCU, where it’s prone to be exposed by fault attacks.
Alternatively, the Ledger-type wallets are resistant to such fault attacks, as the secret is stored in a secure element. But with these, there’s often a significant part of the device firmware and software that remains unavailable for peer review. Thus, a certain trust factor is introduced, which doesn’t quite play well among many crypto enthusiasts.
However, there’s one such hardware wallet that seems to have hit a sweet spot by offering the best of both worlds — providing an SE for storing the secret, while also keeping the firmware and software fully open source.
We’re talking about Coinkite’s Coldcard hardware wallet.
Coldcard Look & Feel
Coldcard has a simple, translucent design for better visual detection of tampering in internal components. The company has focused more on making the devices secure, as well as keeping the manufacturing costs and retail prices low.
It has an OLED screen for displaying information, a 12-key keypad containing numbers 0-9, along with the OK (confirm) and X (reject) buttons. The buttons can be used to enter your Coldcard PIN, navigate through the user interface, and sign transactions.
There’s also a MicroSD card slot (more on that later), 3 indicative LEDs, and a Micro-USB port for power supply & direct connectivity.
For more information on Coldcard hardware, refer to the official documentation.
Why is Coldcard different?
Coldcard is significantly different from the other popular hardware wallets available in the current market.
Secure Element but not “Security Through Obscurity”
Generally, a majority of the hardware wallets with an SE use a dual-chip architecture — a general-purpose MCU used for normal device functions, and a bank-grade SE for storing the secret and signing transactions.
However, the bank-grade SE usually comes along with (partially or fully) closed-source firmware. And the idea is that an attacker cannot exploit the system if they have no knowledge of it. Hence, such type of hardware usually provides “Security Through Obscurity”.
Coldcard also uses a similar dual-chip architecture, but its SE is quite different from the usual one found in Ledger-type hardware wallets.
It uses Microchip’s ATECC508A (Mk2), ATECC608A (Mk3) for storing the critical master secret. This micro-controller is a cryptographic co-processor that provides secure hardware-based key storage. And more importantly, it doesn’t have any closed-source components.
The secure MCU can perform SHA-256 hashing and includes an internal true random number generator (TRNG). Combining the features and careful protocol design, the Coldcard enforces that the attacker must know the specific PIN sequence (which is saved as a part of the wallet set up process) to access the secret.
A Coldcard PIN can be from 4 to 12 digits long, and is split up into 2 parts — prefix and rest PIN — each 2 to 6 digits long. It’s recommended to use a PIN that has at least 8 (4 + 4) digits.
After the prefix PIN is entered, the Coldcard generates two words from the BIP39 wordlist. This pair of words is unique to every Coldcard device & prefix PIN combination and serves as a measure to identify an attempted phishing attack.
If the anti-phishing word pair shown does not match the expected ones, either you entered the wrong prefix PIN or it’s likely a phishing device!
Also, the secure MCU limits the maximum number of PIN attempts — with incremental time delays enforced against repeated PIN attempts — such that a brute force attack is impractical against strong PIN codes.
So, if the attacker now decides to brute force directly into the secret, tough luck there too! The SHA-256 cryptographic hash, along with the TRNG, ensures strong encryption. The search space is now 2^256, and this remains true even when the firmware is fully replaced on the main MCU or the SE chip is removed from the board.
Thus, the ATECCX08A chips rely on the security of cryptographic hash function, rather than “Security Through Obscurity”. The use of such an SE allows Coinkite to keep all of its firmware and software open source, which can be peer-reviewed and verified.
Fully “air-gapped” solution
Coldcard can be operated offline without ever being connected to a computer or mobile device by any means. It does not have Bluetooth or WiFi connectivity support, and you can effectively do everything on the Coldcard by simply plugging it to a power outlet. It can also be optionally operated with a computer via USB.

Coldcard has a MicroSD slot to use a memory card as a medium between the air gap. It can generate skeleton wallets for supported wallet apps including Electrum and Wasabi on the MicroSD card, which contain extended public keys. Extended public keys can be used to generate new receiving addresses, without knowledge of the corresponding private keys.
Coldcard is also the world’s first PSBT-native (”Partially Signed Bitcoin Transaction Format” – BIP 174) hardware wallet; thus allowing you to sign transactions directly on the MicroSD card, and later broadcast them on the network, without the Coldcard being connected.
Other than that, Coldcard can use the MicroSD card for purposes like, backing up the wallet seed into an encrypted file or upgrading the device firmware, all without directly connecting to a computer.
Note: Air gapping provides higher security, but can be a little inconvenient. Coldcard provides the option to choose between more security or more convenience, by supporting both air gapping, as well as direct connection via USB.
No Specialized Software Required
Even if third-party apps are supported, most hardware wallets usually have a dependency on their official companion apps for tasks such as firmware validation & upgrade, extending coin support, etc.
Coldcard doesn’t have a dedicated companion app. It is built to work with native wallet apps like Electrum and Wasabi. And with features like MicroSD support, indicator LEDs, etc., tasks like firmware update & validation can be handled directly within the device.
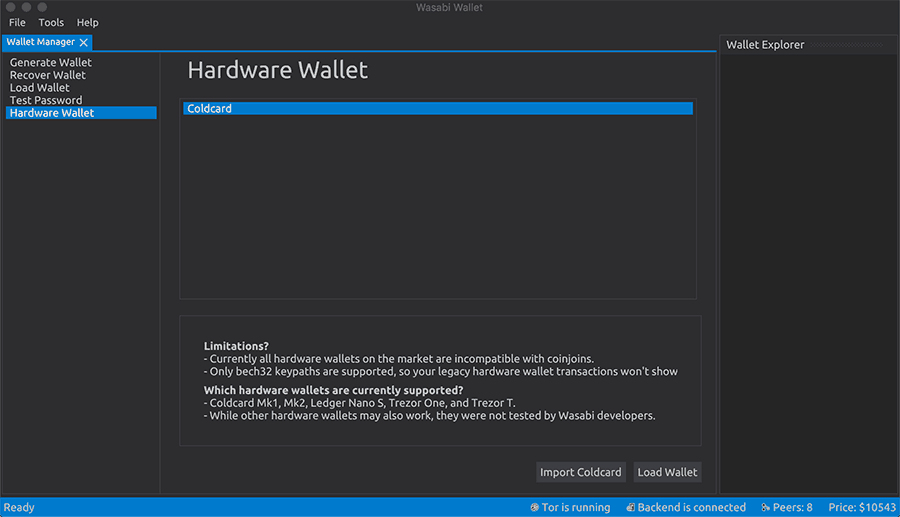
Coldcard works with Electrum and Wasabi both via a direct connection over USB, as well as an air gap solution.
Similarly, firmware updates can be downloaded directly from the Coldcard website and loaded onto the device using Electrum (via USB) or Coldcard itself (via MicroSD card).
Note: As of now, Coldcard only supports Bitcoin (Main & TestNet) and Litecoin (Main & TestNet) cryptocurrencies.
How to set up Coldcard hardware wallet
To improve the device’s security, Coldcard’s set up process is slightly different from that of the other popular hardware wallets. Here’s a step-by-step guide for setting up a new wallet in Coldcard.
Note: Once ordered, your Coldcard should arrive in a sealed bag having a barcode with a number underneath. Inspect the bag for any signs of damage, and report it to Coinkite support if anything is found out of place.
- Power up your Coldcard using a micro-USB wall charger or a battery pack.
- Read through the Terms of use on the Coldcard screen; use the keys 5 (up) or 8 (down) to navigate through the message and press the OK key at the bottom-right to proceed.
- Verify the device serial number and ensure that it matches the serial number printed on the bag.
- Enter the prefix PIN that will be used to protect your Coldcard against unauthorized uses; 4-6 digits recommended.
- Note and memorize the two anti-phishing words displayed on the screen. This word pair is unique to your Coldcard against the specific prefix PIN that you use.
- Enter the rest of your preferred PIN; 4-6 digits recommended.
- Once the PIN has been saved, you should see a menu to create a New Wallet or Import Existing from a BIP39 seed. Navigate up or down using the 5 and 8 keys, and press the OK button.
- With Import Existing, you can enter an existing wallet of yours by providing the corresponding 12-24 word seed.
- Alternatively, when you select New Wallet, a set of 24 seed words will be displayed on the next screen. Scroll through and record every word. You can use the Wallet Backup card provided in the package for this. Finally, press OK to take the quiz and verify that all the words have been recorded correctly.
Once you complete the quiz successfully, your wallet will be ready to use.
Note: Optionally, you can set up a BIP39 passphrase if you wish to switch to a different wallet to store and access your assets.
For more details on how to use the different wallet features, you can check out the Coldcard website.
Coldcard security v/s different attack vectors
Coldcard has taken more than a few measures to ensure the safety and security of their product. Let’s analyze how they hold up against different attack vectors.
Remote Attacks
The Coldcard stores the private keys in a Secure Element chip that encrypts the data using SHA-256 hashing and a TRNG. The SE ensures that the secret is never exposed to the outside world even when you plug the device directly into a computer that is connected to the Internet.
All spend transactions can be verified by reading the OLED display, which shows the receiver’s address, and confirmed by pressing the physical OK key. The only data that is available externally is the signed message used to initiate the transaction.
And if you’re paranoid enough, you can use the Coldcard in air gap mode, where the device always stays offline. In this case, there’s no way to execute remote attacks on the Coldcard hardware wallet.
Physical Attacks
Let’s consider the different types of physical / Man-In-The-Middle (MITM) attacks on the Coldcard wallet.
Supply Chain Attacks
Each Coldcard wallet is packaged in a special serialized bag at the factory. This special bag not only has a tamper-evident seal, but also has a unique serial number, which is also recorded in a secure area of the device’s flash storage, and verifiable during the wallet set up.

Moreover, the use of a clear plastic casing around the Coldcard is an intentional design decision to help easily spot signs of physical tampering within the device’s internals. Also because the plastic case is welded shut, opening and re-sealing the casing for such type of physical tampering is difficult to achieve without being noticed.
Theft
If the device is stolen, it would be difficult (read “impossible”) to gain access to the wallet’s secret. As mentioned before, the secret is stored within the Secure Element, from where it can’t be extracted without knowledge of the correct PIN sequence.
The time limits enforced between wrong PIN attempts make it impractical for carrying out brute-force attacks, especially with the use of strong PIN codes. Moreover, if the attacker tries to brute-force the secret externally without PIN code entry, the SHA-256 hash + TRNG makes brute-forcing unrealistic, due to an enormous (2^256) search space.
Note: In later iterations of the Coldcard (since MK3), a pre-determined number of consecutive wrong PIN attempts will permanently destroy (“brick”) the device and its secret.
Evil Maid Attacks
The Coldcard implements multiple countermeasures to stop evil maid attacks of various kinds:
Malicious Firmware attacks – Ledger STM32 0xF00DBABE
The Ledger Nano S used to suffer from a (presently fixed) serious bootloader issue, in which the firmware verification process involved checking for a specific hex constant (0xF00DBABE) at a particular memory location. This issue was easily exploited by security researchers, and custom firmware was successfully loaded on to the Nano S while writing 0xF00DBABE at a specific memory location.
Unlike the Nano S, the Coldcard Wallet checksums every single flash memory address each time the device is powered up. The SHA-256 hash is calculated and verified against the value stored securely within the SE. The result is shown to the user with red (for false) and green (for true) lights that cannot be accessed by any part of the system other than the SE.
When you perform a firmware upgrade, the SHA-256 hash value for the new firmware changes. At that time, the new “should be” hash value is also written to the SE. If an attacker wishes to flash a custom (malicious) firmware, they must know the primary device PIN.
Tempest attacks – Ledger Blue RF leaks
During another demonstration, security researchers were able to determine the Ledger Blue PIN code by tracking the radio frequency signals generated due to the touches registered on different areas on the device’s screen. This is difficult to execute on the Coldcard, as its firmware has necessary protections in place against these kinds of attacks.
Additionally, since the MK2 version, Coldcard uses physical keys instead of touch keys, thus strengthening tempest-resistant features.
Fault attacks – TREZOR One Glitching
The TREZOR devices are prone to fault attacks, as the secrets are stored (in an encrypted form) on the main general-purpose MCU itself. Such is not the case with Coldcard, where all the secrets are stored in the ATECCX08A SE chip.
As discussed before, extracting data from this SE is impossible without the knowledge of the primary PIN code. It’s also resistant to brute force attacks with features like enforced timed delays between unsuccessful PIN attempts and SHA-256 hashing of the secret with a TRNG.
On top of that, Coldcard also makes it easy to detect possible MITM attacks, without giving away your full PIN code. After entering the prefix PIN, it displays two anti-phishing words, which are unique to your device and the prefix PIN combination. If the words do not match, that suggests your Coldcard hardware has likely been tampered with.
Alternatively, any attempts to flash a malicious version of the device firmware (without knowing the primary PIN) would be identified during the checksum verification (red & green lights) while the device is powered up.
The “$5 Wrench” Situation

All security mechanisms employed within a hardware wallet arguably fail when you’re under duress, for example, held at gun-point to reveal the device PIN and/or transfer Bitcoins to the attacker’s wallet. Features such as BIP39 Passphrase support, Duress PIN and BrickMe PIN enables you to bail out or destroy your Coldcard wallet in such situations.
Passphrase
The BIP 39 standard supports an optional passphrase in addition to the 24-word seed, which gives access to a new wallet for every possible passphrase. The Coldcard wallet supports adding a passphrase to the initial seed words, beginning with firmware version 2.0.0.
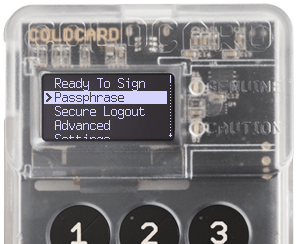
When you log in to the Coldcard at any time by entering the PIN, the default passphrase is always empty. To add a passphrase and access an entirely new wallet associated with it, do the following:
- Login to the Coldcard using your prefix & rest PIN.
- Select Passphrase from the Coldcard menu.
- Press OK on the Passphrase description screen.
- Add a new passphrase by selecting the appropriate options: Edit Phrase (enter characters by moving up/down & left/right), Add Word (choose a word from the BIP39 word list), Add Numbers (enter up to 32 numeric digits using the physical keypad).
All of these options can be combined. Your passphrase may contain a word from the BIP39 word list, followed by a few numbers, and then some special characters as well. The phrase can be up to 100 characters long.
The Passphrase menu also has the option to Clear All, in case you need to start over entering the passphrase or wish to go back to your 24-word seed wallet.
Once you’ve selected the passphrase, choose Apply from the menu to proceed. An eight-digit wallet fingerprint will be displayed on the screen. This fingerprint may be used to verify that the wallet accessed by entering the specific passphrase, is indeed the wallet that you intended to open. The wallet fingerprint should be the same every time you enter the same passphrase.
Duress Wallets
A duress wallet is supposed to act as an escape route in case of duress situations when you’re forced to reveal a PIN. You can enter the Duress PIN instead of the actual PIN to access a different wallet.
When a Duress PIN is entered, Coldcard acts normally and unlocks the wallet, so that attackers are not usually alerted. But, people familiar with the Coldcard might be able to tell the difference. For example, duress wallets do not have the Passphrase menu item.
BrickMe PIN
The Coldcard additionally lets you set a BrickMe PIN to effectively destroy the Coldcard device permanently. When the BrickMe PIN is used, the critical secret is irreversibly destroyed, and the wallet essentially becomes as useless as a brick”.
Both the Duress PIN and BrickMe PIN can be set via the Settings menu (Change PIN Code option) in Coldcard wallet.
Bonus: Set up Coldcard in the most secure way possible
These tips will help you to set up your Coldcard wallet with maximum security.
Power-up without a Computer: Plug in the Coldcard to a wall socket or a battery pack to power it up.
Strong 12-digit PIN: Create a strong PIN code with 6-digits of prefix PIN and 6-digits of rest PIN. And then, create a new wallet and record your seed securely for recovery purposes.
Passphrase Setup: Next, go to the Passphrase menu and set a strong passphrase that you can remember, yet not easy to guess. Once you apply the passphrase, you’ll be logged into the particular passphrase associated wallet. Also, note the wallet fingerprint for future reference.
PSBT: Now, store or transfer your assets into the passphrase-associated wallet via PSBT, using a MicroSD card.
Always Offline: Continue using the Coldcard Wallet in air gap mode.
Note: Though Coldcard has a Duress Wallet specifically for duress situations, we don’t recommend you use the feature, as an attacker familiar with Coldcard can easily detect the difference between an actual wallet and a duress one. Instead, you might want to load some funds (that you’re willing to lose) in the primary wallet without the passphrase, which you can access in duress situations.
Additional Tip: The new Coldcard MK3 has a feature to automatically “brick” the device after 13 consecutive failed PIN attempts. But, if you’re using an earlier version of the device, you can set a BrickMe PIN that has the same number of digits as your primary PIN, but of a smaller numeric value. That way, while brute-forcing your PIN code, the attacker might just brick the device before unlocking it.
Should you get a Coldcard
At this moment, Coldcard doesn’t support multiple currencies. And it isn’t ideal for sending Bitcoins while on-the-go. In spite of these, Coldcard may be the perfect solution for long-term Bitcoin “hodlers”.
With its main focus on security & cost-effectiveness, the device is an ideal choice for people looking to store Bitcoins in the most secure way (air gap, Secure Element), without compromising on the open-source ideology.